Reading ENISA Threat Landscape Report 2018
The annual ENISA Threat Landscape report for 2018 is out! The report focuses on the threat landscape changes and developments in motives and tactics of the most important threat agent groups, namely cyber-criminals and state-sponsored actors.
This annual deliverable of ENISA is a great read for CTI practitioners and information security professional worldwide. The sections 2 and 6 of the report are a must read for CTI practitioners. Section 2 focuses on “CTI state of play” and includes a Cyberthreat Intelligence Maturity Model. Section 6 includes all the conclusions that derived from ENISA’s threat analysis team throughout the year. Conclusions also provide tangible recommendations for businesses, policy makers, technical professionals as well as professionals in academia. Finally, it is interesting to see ENISA’s Threat Analysis team to analyse Misinformation/Disinformation threat in Section 5.
It was fascinating contributing to this report and being one of the authors (among others). I hope you enjoy it and provide your feedback to European Union Agency for Network and Information Security (ENISA) threat team.
Top 15 Cyber Threats
The report highlights some of the main trends relating to cyber threats in 2018:
- Mail and phishing messages have become the primary malware infection vector;
- Crypto-miners have become an important monetisation vector for cyber-criminals;
- State-sponsored agents increasingly target banks by using attack-vectors utilised in cyber-crime;
- The emergence of IoT environments will remain a concern due to missing protection mechanisms in low-end IoT devices and services. The need for generic IoT protection architectures/good practices remains a pressing issue;
- Cyber threat intelligence needs to respond to increasingly automated attacks through novel approaches to the use of automated tools and skills.
- Skills and training are the main focus of defenders. Public organisations struggle with staff retention due to strong competition with industry in attracting cybersecurity talents.
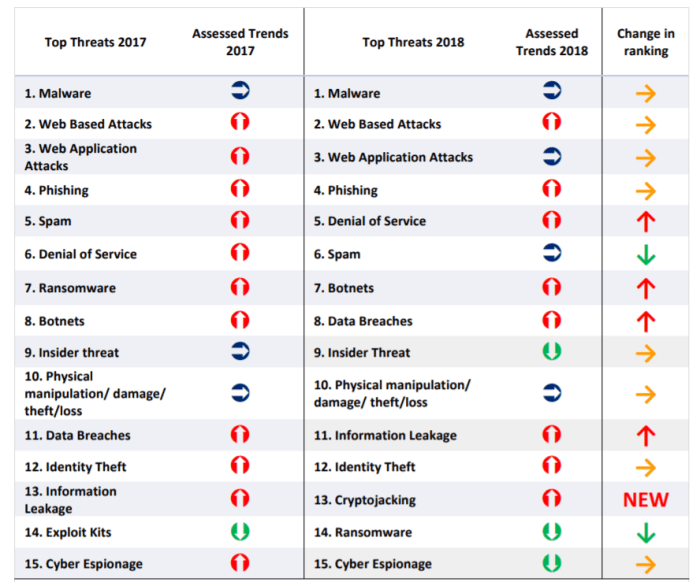
Τhe report lists the Top 15 Threats 2018 including detailed information on trends and observed evolution as seen below:
Policy Conclusions
The report lists some conclusions related to policy.
- The EU will need to develop capabilities (human and technical) to address the needs for CTI knowledge management. EU Member States are requested to introduce measures to increase its independence from currently available CTI sources (mostly from outside the EU) and enhance the quality of CTI by adding a European context.
- As CTI is perceived as a public good, capabilities will be required to offer “baseline CTI” to all interested organisations. EU governments and public administrations are requested to share “baseline CTI”, covering sectorial and low-maturity needs of organizations.
- Regulatory barriers to collect CTI exists and should be removed. Coordinated efforts among EU Member States is required in the collection and analysis of CTI, as crucial activity in the implementation of proper defence strategies.
Business conclusions
The report also lists some of the analysis’ conclusions related to businesses.
- Businesses will need to work towards making CTI available to a large number of stakeholders, with focus on the ones that lack technical knowledge. The security software industry needs to research and develop solutions using automation and knowledge engineering, helping end-users and organizations mitigating most of the low-end automated cyberthreats, with minimum human intervention.
- Businesses will need to take into account emerging supply chain threats and risks. The technology industry needs to introduce qualitative measures into its production processes, perform end-to-end security assessments and adhere to certification schemes.
- Businesses will need to bridge the gap in security knowledge among the operated services and end-users of the service. The consumption of CTI knowledge is a major step to achieve this goal.
Technical/research/educational conclusions
Some technical, research and educational conclusions are also analysed in the report:
- The ingestion of CTI knowledge needs to be enlarged to include accurate information on incidents and information from related disciplines. CTI vendors and researchers have to find ways to enlarge the scope of CTI, while reducing necessary manual activities.
- CTI knowledge management needs to be the subject of standardisation efforts. Of particular importance are the developments of standard vocabularies, standard attack repositories, automated information collection methods and knowledge management processes.
- Research needs to be conducted to better understand attack practices, malware evolution, malicious infrastructure evolution and threat agent profiling. Advances in those areas may significantly reduce exposure to cyberthreats and advance CTI practices.
- Much more training offerings need to be developed in order to satisfy the current market needs in CTI training.
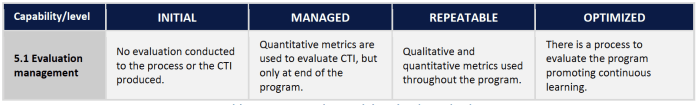
Cyberthreat Intelligence Maturity Model
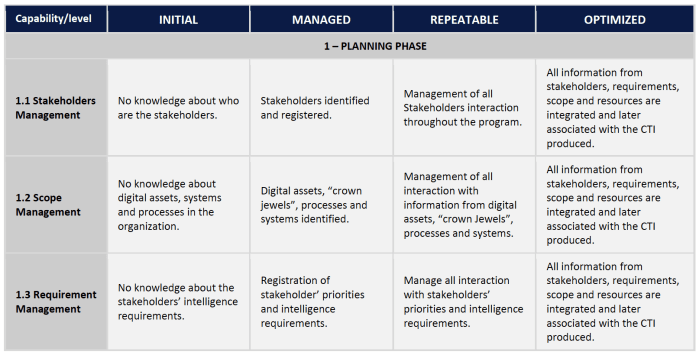
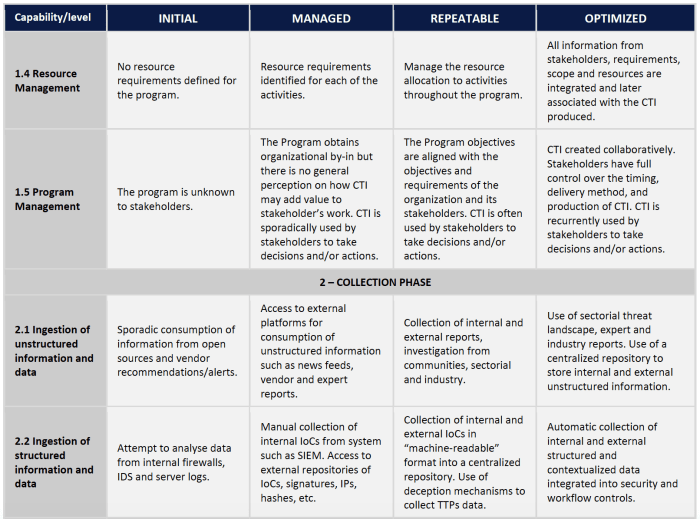
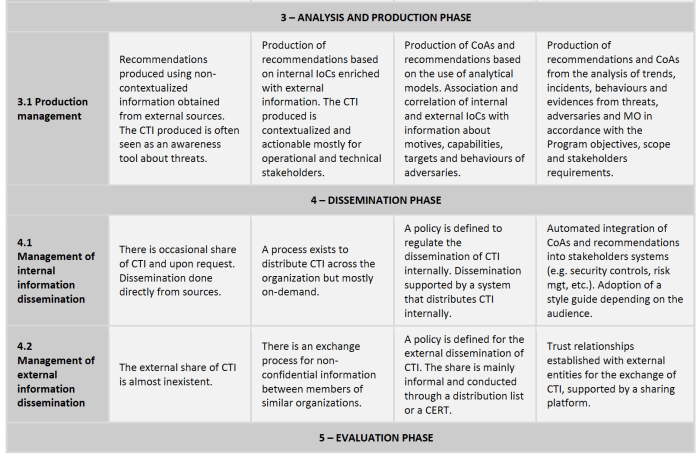
The report also provides a Cyberthreat Intelligence Maturity Model. The following table maps the evaluation criteria defined to the levels and capabilities of the maturity model provided:
Happy reading!
Link to ENISA’s report: https://www.enisa.europa.eu/publications/enisa-threat-landscape-report-2018