During the past week CrowdStrike published its 2018 Mid-Year Review call “Observation from the front lines of threat hunting“. This report provides insights, trends and details on today’s most sophisticated cyber attacks observed by CrowdStrike Falcon OverWatch team.
Some interesting points of the report include:
- Crowdstrike provides a useful heatmap that shows the number of intrusion cases attributed to an adversary by industry vertical.

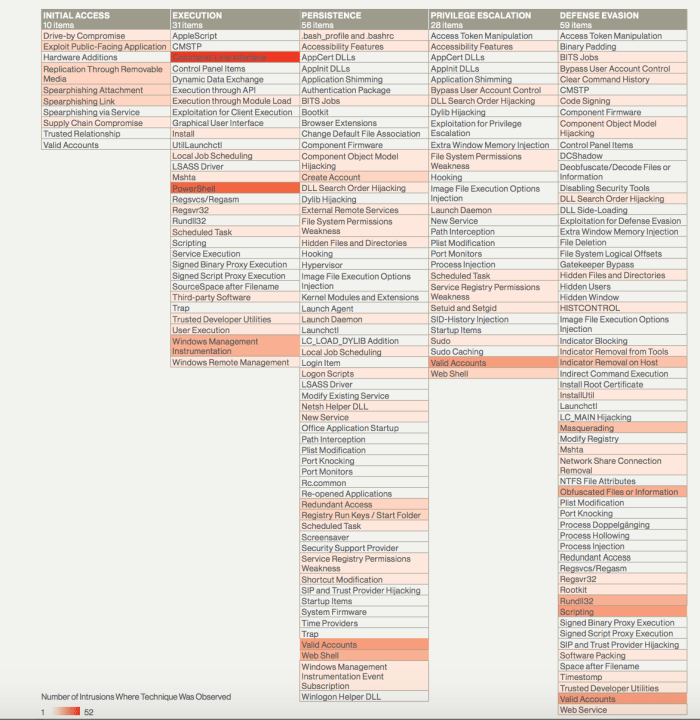
- Observed intrusions mapped to MITRE ATT&CK framework (H1 2018)

- E-crime actors show increasing interest in cryptocurrency mining. Actors also employed techniques that allowed them to perform extensive lateral movement (via PsExec), creating as large a foothold as they could to commandeer mining resources.

- Crowdstrike highlighted the blurring of lines between the TTPs of highly skilled nation-state adversaries and their criminally motivated counterparts. One specific manner in which this recurring trend was observed was with the malicious use of TeamViewer software.
- Actors also use a variety of defense evasion techniques as shown below:

- Observed trend of threat actors gaining access via RDP by leveraging valid credentials. This is also observed by FBI and DHS that released a joint report called: “CYBER ACTORS INCREASINGLY EXPLOIT THE REMOTE DESKTOP PROTOCOL TO CONDUCT MALICIOUS ACTIVITY” .
- Actors steal credentials employing several TTPs: Kerberoasting, credential dumping and through GPP files.
Enjoy and thanks to CrowdStrike for the insightful report!